+91 92204 69008
Server & Endpoint Security
Aquacodes provides robust server and endpoint security services, safeguarding your systems against cyber threats. Utilizing advanced monitoring, real-time threat detection, and proactive vulnerability management, we ensure data protection, minimize risks, and maintain business continuity. Our solutions deliver comprehensive defense for your critical infrastructure and endpoints.
Server & Endpoint Security Enquiry Form


Continuously monitors endpoint activities to detect suspicious behavior in real time. EDR enables rapid threat investigation, root-cause analysis, and automated response to contain attacks before they spread across the network.

XDR unifies security across endpoints, servers, networks, and email systems into a single platform. It correlates data from multiple sources to provide deeper visibility, faster threat detection, and coordinated response to advanced cyber threats.

MDR provides 24/7 expert-led threat monitoring and response services. Security specialists actively hunt, detect, and respond to threats on your behalf, reducing the burden on internal teams while improving overall security posture.

Comprehensive protection for desktops, laptops, and servers against malware, ransomware, and zero-day attacks. Includes antivirus, behavioral analysis, exploit prevention, and system hardening to secure all critical computing environments.

Protects smartphones and tablets from threats such as malicious apps, phishing, and data leakage. Features include device control, app scanning, secure access, and policy enforcement for both corporate and BYOD environments.

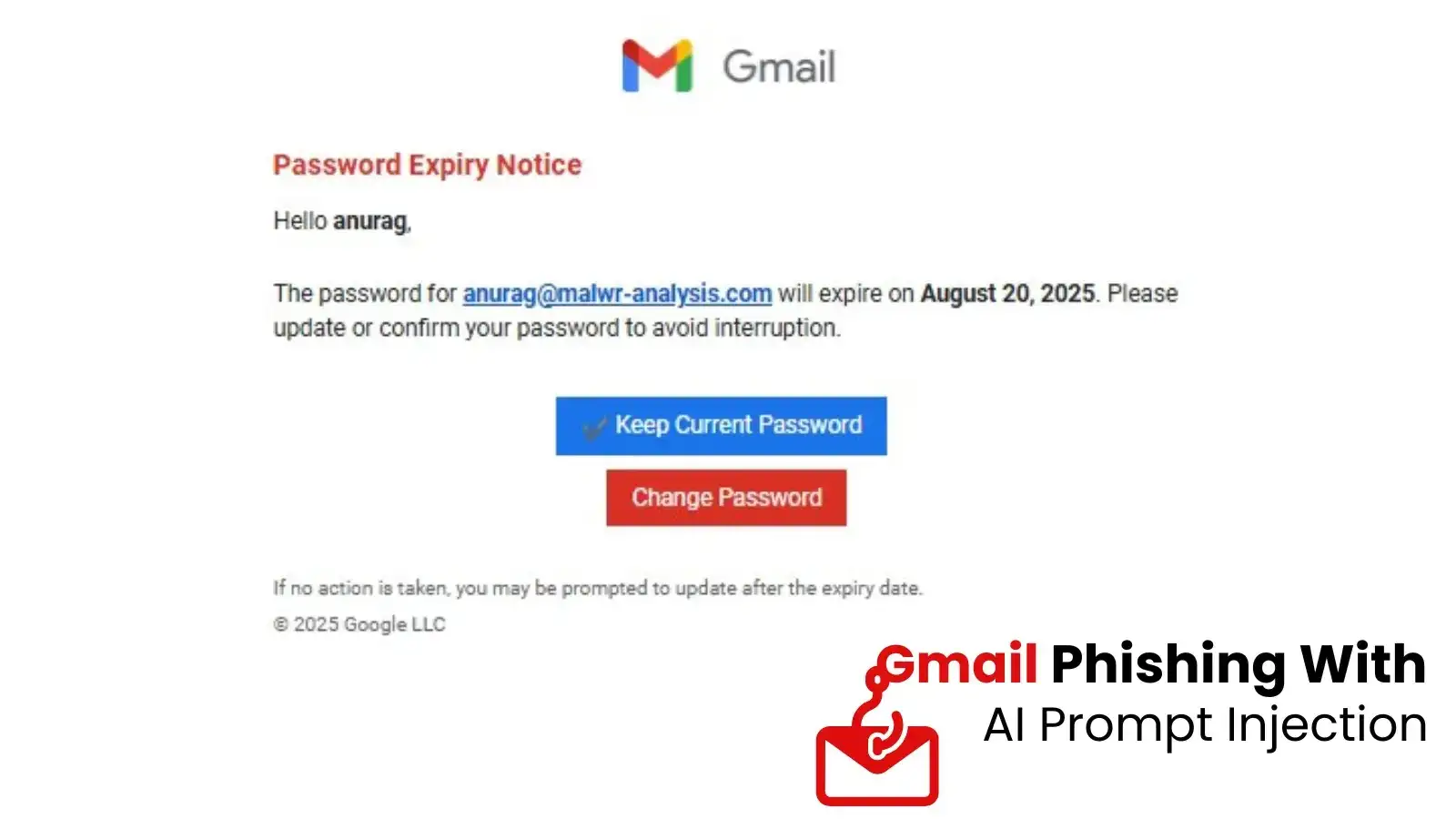
Defends against phishing, spam, malware attachments, and business email compromise (BEC). Advanced filtering, sandboxing, and link protection ensure safe email communication and prevent entry points for cyberattacks.

Detects and blocks ransomware attacks using behavior-based analysis and rollback mechanisms. Ensures critical data remains protected and recoverable, minimizing business disruption and financial impact.

Prevents unauthorized access, sharing, or transfer of sensitive data. DLP policies monitor and control data across endpoints, email, and cloud applications, ensuring compliance and data confidentiality.

Provides a unified dashboard to manage all endpoints, policies, and security events. Offers real-time insights, reporting, and analytics to help organizations make informed decisions and respond quickly to emerging threats.